Security policies rarely fail because of technical problems, but rather due to organizational challenges.
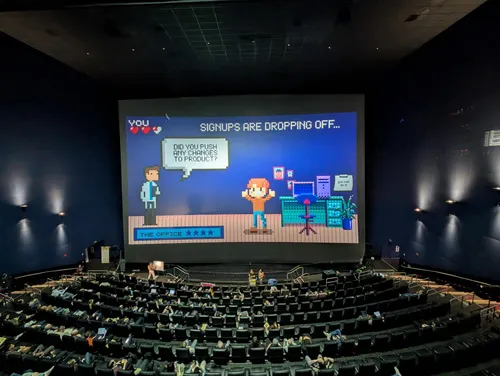
BSidesSF plays incident response | BSidesSF 2025 | with Whitney Merrill
- Incident Response
As Incident Commander, team up with your product and privacy leads to navigate the response. You decide what to do in this choose-your-adventure talk.
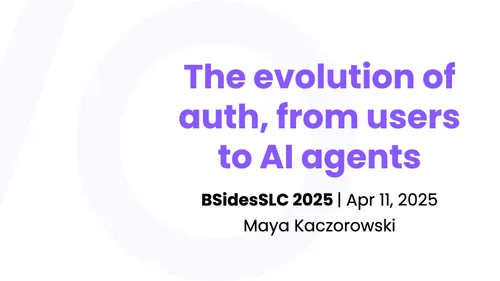
Although painful, authentication failures can help us improve — as long as we actually apply those lessons.
Authentication has transformed from passwords to passkeys. We’ll look back in time and predict what’s next.
Panel: Mastering the Technical Requirements for FedRAMP | Chainguard Assemble 2025
- Compliance
- Panel
FedRAMP deadline? Come learn how companies handle FIPS & monitoring requirements while balancing feature delivery.
OAuth Works for AI Agents, but Scaling Is Another Question | The New Stack Makers
- Podcast
- AI agent
- OAuth
- Identity
As AI agents proliferate, the “exponential” scaling may require new ways of managing authorizations, said Maya Kaczorowski of Oblique in this episode of Makers.
I interviewed 57 security leaders about what sucks in security. Top pain points: inconsistent access management, vulnerability remediation, and SaaS logs.
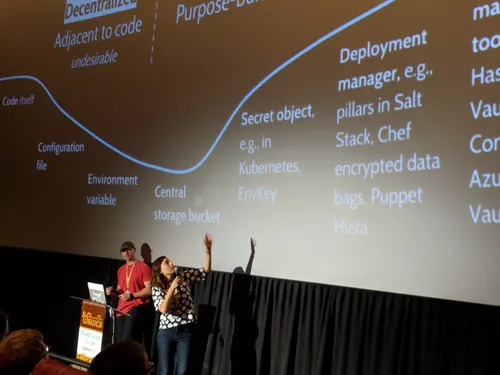
Panel: Secrets and Policies — Automating Cybersecurity | PulumiUP 2024
- Infrastructure Security
- Panel
Discover how to balance security and business agility through secrets management, automation, and supply chain security.
Want to start a security company but need an idea? Here are 5 startups that should exist — complete with problems to solve, buyers, and how to build them.
How Tailscale Builds for Users of All Tiers | Screaming in the Cloud
- Product management
- Open source
- Podcast
Maya shares insights on Tailscale’s product approach and how it serves users from free tier to enterprise, exploring what makes their approach distinctive.
So what does a product manager do, exactly? | Women of Silicon Roundabout 2023
- Product management
You might have experience working on a product in some capacity, and with a product manager… but what do they do, exactly?
Product launches are both exciting and nerve-wracking. Learn how to find the sweet spot between rapid shipping and sustainable quality for your team.
Developers want speed, security teams want caution — learn how to reduce friction between teams by choosing tools that serve both needs.
The Importance of Cutting-Edge Security and How To Combat Data Breaches | Women Impact Tech
- Security programs
- Panel
A discussion on protecting valuable data in the cloud, covering visibility, accessibility and risk management to prevent security breaches and data theft.
Securing user to server access in Kubernetes | CloudNativeSecurityCon NA 2023 | with Maisem Ali
- Container security
- Remote access
How should you secure access to internal Kubernetes services? We’ll explore authentication, authorization, load balancing, and encryption options.
Cloud-Native Network Security Panel | Tailscale and ControlPlane meetup
- Container Security
- Remote access
- Panel
A panel discussion exploring cloud-native network security, featuring insights from engineering and security leaders at Tetrate, Tailscale, and ControlPlane.
Maya Kaczorowski (@MayaKaczorowski, Product @Tailscale) talks about the new world of remote systems access, zero-config VPNs, and why everyone loves using Tailscale.
Demistifying Risks for Dev-Focused Companies | Accel DX 2022
- Supply chain security
- Infrastructure security
- DevOps
- Panel
With the movement towards CI/CD, new code written by developers is deployed continuously at sophisticated companies. However, security practices haven’t kept up. As leaders in the space, Chainguard’s Kim Lewandowksi, Snyk’s Randall Degges, and Tailscale’s Maya Kaczorowski are not strangers to these challenges. In a panel moderated by Accel’s Casey Aylward, they will discuss security resources for developers, and how to understand and effectively apply them before it’s too late.
Tailscale SSH Aims To Simplify And Secure Remote Connections | TFiR Let's Talk
- Remote access
- Podcast
In this episode of TFiR Let’s Talk, Swapnil Bhartiya sits down with Maya Kaczorowski, Product Manager at Tailscale, to discuss Tailscale SSH in beta and how it simplifies remote connections, taking away the need for SSH keys. She explains the motivation behind creating Tailscale SSH and what sticking points it is tackling.
The Past, Present, and Future of Supply Chain Security | ACM Tech Talk
- Supply chain security
- Moderator
Explore 40 years of software supply chain security evolution and modern mitigation techniques for both open source and proprietary development.
WireGuard from the ground up | BSidesSF 2022 | with David Crawshaw
- Remote access
- Encryption
Understand WireGuard’s end-to-end encrypted traffic, protocol implementation and cryptography, with comparisons to IPsec, ngrok, and OpenVPN.
The road to BeyondCorp is paved with good intentions | NorthSec 2022 | with Eric Chiang
- Remote access
- BeyondCorp
BeyondCorp kicked off zero trust, but there’s more hype than help on actually implementing it. We’ll share real insights on making it work for your org.
Panel discussion and Q&A on detection and response.
Remote development can improve your developers remote work experience | DevX Conf 2022
- Remote access
- DevOps
Developing remotely is different from working remotely — we’ll explore how remote development practices can actually help overcome remote work challenges.
DevOps goals haven’t changed, but everything else has — our tools, infrastructure, and how we work. Here’s how to prepare for what’s next.
Software composition analysis identifies dependencies in shipping software — learn about finding vulnerabilities, licenses, and metadata in your code.
How secure is your software? Carl and Richard talk to Maya Kaczorowski of GitHub about The State of the Octoverse Security Report — one of three annual reports coming from GitHub about how software is being built.
One library in your manifest can bring in a huge dependency tree. How do we track vulnerabilities and keep dependencies up to date?
As a maintainer of your open-source project, what can, and should you be doing to improve your project’s security?
Dependency Review shows you a rich diff of dependency manifest changes while reviewing pull requests, letting you see exactly what’s changed.
Catching vulnerabilities early with GitHub | GitHub Universe 2020 | with William Bartholomew
- Supply chain security
Want to catch security issues earlier? Learn how GitHub’s Dependency Graph and Dependabot help you shift left and stay on top of vulnerabilities.
A panel that doesn’t suck about security, from multiple perspectives. Categories, organisations and security practices are being reinvented, but what does it look like from the practitioner perspective?
How Mettle uses GitHub to secure their software supply chain | GitHub Talk | with Mikail Tunç
- Supply chain security
Following DevSecOps means approaching security as an ongoing part of software development — and staying up to date on the code your software depends on. Join Mikail Tunç, Principal AppSec Engineer at Mettle, and Maya Kaczorowski, GitHub Product Manager for an in-depth conversation into how Mettle uses GitHub’s application security capabilities to understand which dependencies they use, their vulnerabilities, how to patch them — and get back to work.
La sécurité dans tous ses états — la chaine d’approvisionnement logicielle et l’open source | Electro Monkeys
- Podcast
- Container security
- Supply chain security
- Open source security
- French
La sécurité est un aspect fondamental et pourtant souvent négligé de nos systèmes d’information. Le code est la base de code sont aujourd’hui au coeur de toute entreprise technologique. Mais alors quels sont les problèmes soulevés, quelles solutions y apporter et avec quels outils ?
How Nutanix uses GitHub to secure their software supply chain | GitHub Talk | with Jon Kohler
- Supply chain security
Following DevSecOps means approaching security as an ongoing part of software development — and staying up to date on the code your software depends on. Join Jon Kohler, Nutanix Technical Director, and GitHub Product Manager Maya Kaczorowski for an in-depth conversation into how Nutanix uses Dependabot and the GitHub dependency graph to understand which dependencies they use, their vulnerabilities, how to patch them — and get back to work.
Software Supply Chain Security and Puzzles | The POPCAST with Dan POP
- Software supply chain security
- Puzzles
- Podcast
Episode 23 - GitHub’s Maya Kaczorowski on Software Supply Chain Security and Puzzles!
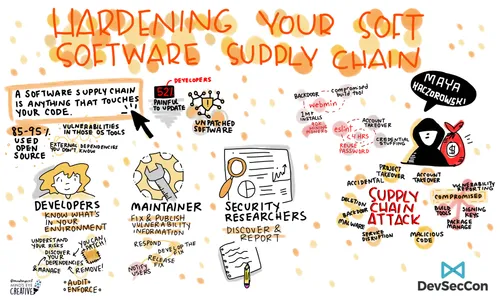
Hardening your soft software supply chain | DevSecCon 2020
- Supply chain security
- DevSecOps
Open source code means anyone can contribute — even attackers. Learn about real supply chain attacks and how to secure your dependencies.
Maya joins Cornelia’s keynote to share key ways in which GitOps can contribute to your security needs.
Learn how GitHub helps teams understand code vulnerabilities and manage patches to secure their software supply chain, with practical steps to get started.
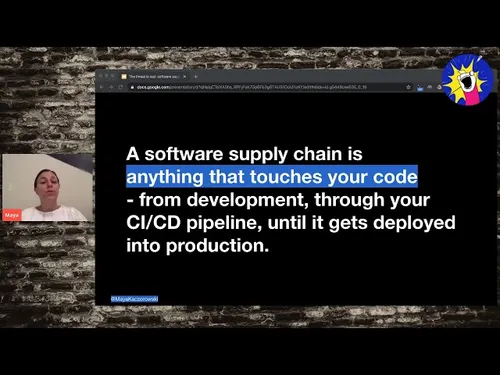
The threat is real: software supply chain vulnerabilities | AllTheTalks.online
- Supply chain security
Software supply chain threats are real! What’s actually happening in the wild, how do you determine your dependencies, and properly secure yourself?
Cryptic Dependencies & Cryptic Crosswords | PancakesCon 2020: Quarantine Edition
- Supply chain security
- Puzzles
How do you determine your code’s cryptic dependencies, and what should you do when a new vulnerability is discovered? And how do you solve cryptic crosswords?
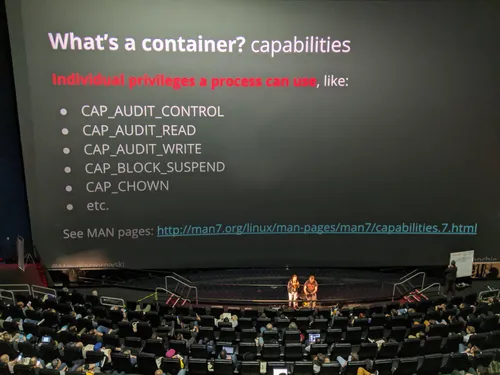
Checking your —privileged container | BSidesSF 2020 | with Sam "Frenchie" Stewart
- Container security
A look under the hood at Docker’s —privileged flag: how Docker isolation really works, what happens when it’s disabled, and why it leads to container escapes.
Container and orchestration security | Application Security Podcast
- Podcast
- Container security
Maya joins us to discuss how containers improve security, a high-level threat model of containers and orchestration, and tips for enhancing security as you role out containers and Kubernetes.
How Kubernetes Components Communicate Securely in Your Cluster | KubeCon North America 2019
- Container security
How do your cluster components talk to each other? Understand what authentication, integrity, and encryption protections exist for cluster communications.
Shifting Cloud Native Security All the Way Left | The New Stack Pancake Breakfast at KubeCon
- Container security
- Panel
Many IT teams begin moving their applications to containers and Kubernetes after their managers mandate the switch. Then in the rush to deploy they may forget, or simply delay, some fundamentals. Only six to 12 months later does integrating security into their CI/CD pipeline becomes a priority. This gradual evolution toward cloud native security best practices is worrisome, but it’s the norm among organizations adopting Kubernetes today. This is what we learned from a panel of cloud native security experts at The New Stack’s pancake and podcast from KubeCon+CloudNativeCon North America this week.
Who’s responsible when open source security goes wrong? See how mature projects handle dependencies, incidents, vulnerabilities and bug bounties.
Does eating ice cream slower prevent a brain freeze?
Containers can actually improve your security story | O'Reilly Velocity 2019
- Container security
Maya Kaczorowski covers how containers change your development pipeline and how this helps, rather than hurts, your overall security model.
Google Product Manager, Dustin Kirkland interviews Google Product Manager, Maya Kaczorowski to discuss interesting vulnerabilities in the Kubernetes space.
Container Forensics: What to do when your cluster is a cluster | KubeCon Europe 2019 | with Ann Wallace
- Container security
Get cluster visibility through logs and tools, connect your infrastructure data, and implement container mitigations and response.
Exploring The Latest in Public Cloud Providers | The New Stack at KubeCon
- Container security
- Interview
We’re live from #CloudNativeSecDay for a conversation with TNS Founder & EiC Alex Williams & Google Product Manager Maya Kaczorowski to explore all the latest in public cloud providers today from #KubeCon Barcelona.
In today’s show we discuss the attack surface of a managed Kubernetes service.
Listen to this very insightful episode with special guest from Google, Maya Kaczorowski, as she discusses container security with BMC Solutions Architect, Ajoy Kumar.
Who Protects What? Shared Security in GKE | Google Cloud Next '19 | with Jesse Endahl
- Container security
In GKE, the control plane is managed by Google, and the nodes by users — how does this split responsibility apply for security updates and incidents?
What containers are and how they change your security model | Google Cloud Security Talks at RSA 2019
- Container security
A practical overview of container and Kubernetes security fundamentals and how to protect them, including security features available on Google Cloud.
You might still need patches for your denim, but you no longer need them for prod | BSidesSF 2019 | with Dan Lorenc
- Container security
In this talk, Maya and Dan will cover what changes in your patch management story if you use containers instead of virtual machines in production.
This Year, It’s About Security | KubeCon North America 2018 | with Brandon Baker
- Container security
Kubernetes has made giant strides in 2018 to improve security for end users. Here’s an overview of what’s happened in 2018.
Learn how to use network security controls for your containers | Cloud OnAir | with Manjot Pahwa
- Container security
Learn how you can segment containers in a network, what traffic flows you should allow and how to maintain the security of your container network.
The State of your Supply Chain | KubeCon China 2018 | with Andy Martin
- Container security
- Supply chain security
Dive deep into container software supply chain security tools, from Grafeas to Notary, including how to identify and automatically remediate vulnerable images.
Turtles All the Way Down: Managing Kubernetes Secrets with Secrets | KubeCon China 2018 | with Alexandr Tcherniakhovski
- Container security
Secrets are the cornerstones of Kubernetes’ security model; used both by Kubernetes itself and by users. We’ll explore options for protecting these secrets.
Containers are making it easier for developers to build and deliver applications in the cloud. However, managing risk around container deployments remains a significant challenge for security teams. Join this session to learn about the security challenges around container deployments and best practices to follow while securing containers.
Unravel the mystery of container security | Cloud OnAir | with Sandra Guo and Juan Oviedo
- Container security
Containers are increasingly used to deploy applications, with benefits of portability, scalability and lower management. Yet their security remains unclear.
Let’s talk container security! This week, Melanie and Mark learn all about the three main pillars of container security and more with our guest, Maya Kaczorowski.
Google Infrastructure Security | Video tour
- Infrastructure security
- Encryption
- Interview
Did you know that Google has invested $30.9 billion to build out our global infrastructure over the past 3 years? Learn more about Google’s infrastructure security through a tour with product manager Maya Kaczorowski and developer advocate Cassie Kozyrkov.
How Google Protects Your Data at Rest and in Transit | Google Cloud Next '18 | with Il-Sung Lee
- Encryption
An overview of data protection on Google Cloud: encryption at rest and in transit, network layer security, and advanced protection options like IPsec and istio.
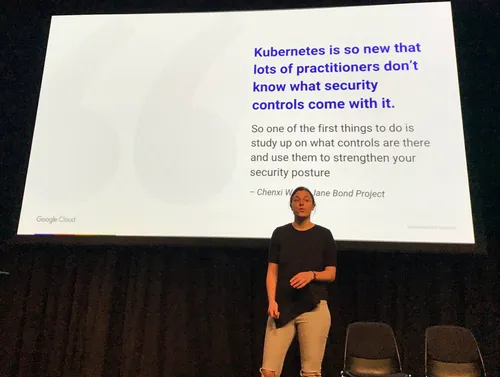
Kubernetes for Enterprise Security Requirements | Google Cloud Next '18 | with Jesse Endahl
- Container security
Learn how enterprises meet security requirements for container workloads in production, with examples from Kubernetes features and Fleetsmith’s approach.
Google Infrastructure Tour | Google Cloud Next '18 Showcase
- Infrastructure security
- Encryption
- Interview
Follow our Showcase reporters they tour the venue and get the inside scoop on Google Cloud Next ‘18 products.
DevSecOps: Developers play security offense | Threat Actions This Week
- Podcast
- Panel
- DevSecOps
We look for the balance between developers’ security responsibility and the security team. Maya Kaczorowski from Google, Shannon Lietz from Intuit and Larry Maccherone from Comcast help weigh the options.
On this week’s Kubernetes Podcast, your hosts talk to Maya Kaczorowski from Google Cloud about Kubernetes security, and look at announcements from Microsoft, Docker, Cisco and Spotify.
Maya Kaczorowski works on container security at Google. In a recent talk at KubeCon, Maya discussed runtime security of containers on Kubernetes. Maya joins the show to discuss container security, and what it means to software developers and operators.
Engineering Container Security: Addressing the Unique Security Challenges of Containers at Scale in a Multi-Cloud World | OpenStack Summit 2018
- Container security
- Panel
With container adoption on the rise, new security strategies are needed to address the unique challenges that containers represent. In this panel discussion, container experts will discuss the security risks of containers and briefly examine many of the multiple approaches that can be taken to achieve security in a container-based environment and a hybrid cloud world.
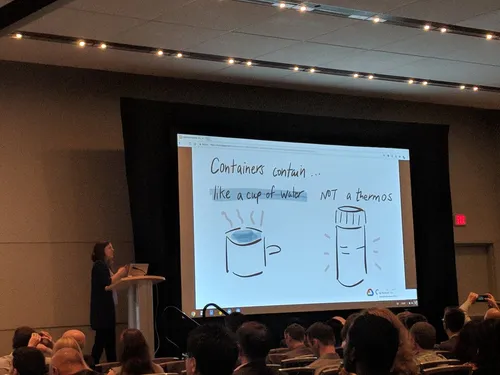
Container infrastructure keynote: Containers Should Contain …Right? | OpenStack Summit 2018
- Container security
- Keynote
Containers are popular for deploying apps due to portability and scalability, but let’s be clear — they don’t provide an impermeable security boundary.
As public cloud adoption continues to accelerate, security becomes a top priority for many organizations. Maya Kaczorowski, Product Manager at Google Container Security explains what security consisted of in legacy systems. We then talked about the security panorama in the cloud, specifically in containerized applications. Maya explained various security risks in these applications as well as solutions. One of these is gVisor, a new open source sandbox that provides secure isolation for containers.
Kubernetes Runtime Security: What Happens if a Container Goes Bad? | KubeCon Europe 2018 | with Jen Tong
- Container security
Runtime security is about mitigating impact and damage that can occur when your container deployment is compromised.
Using containers, enterprises now have strong, secure-by-default primitives available for deploying apps to their infrastructure. Containers are enabling organizations to adopt better engineering practices like immutable infrastructure — increasing deployment agility and reducing mean time to patch. Companies are thinking strategically about to securely manage their software supply chains. Moderated by eWeek’s Senior Editor, Sean Michael Kerner, collaborators in the container ecosystem will share how containers are revolutionizing the way apps are secured and how we can expect container security to evolve in the future. The panel will also touch on open source projects Notary, TUF, SPIFFE, and OPA.
Cloud SCC container security partners | Google Cloud at KubeCon
- Container security
- Interview
At KubeCon + CloudNativeCon Copenhagen we announced that five container security companies have integrated their tools with the Cloud Security Command Center to help you better secure the containers you’re running on Kubernetes Engine. Our PM in container security, Maya Kaczorowski, will meet them to discuss their technical integrations.
Securing #Kubernetes | The New Stack Pancake Breakfast at KubeCon
- Container security
- Panel
To do cloud-native computing, you need to identify all your workloads, and, more importantly, they need the ability to identify each other, so they can work together in automated chains. To aid in this task, the Cloud Native Computing Foundation has adopted the open source SPIFFE specification, and its associated SPIRE runtime. SPIFFE provides a standard for securely identifying software components in heterogeneous IT systems and SPIRE is the engine that can make it happen (and, in this setup, CNCF’s Open Policy Agent [OPA] can enforce the authorization duties).
Exploring Container Security: detect and manage an attack | Google Cloud at KubeCon
- Container security
- Interview
You’ll soon be able to manage security alerts for your clusters in Cloud Security Command Center (Cloud SCC), a central place on Google Cloud Platform (GCP) to unify, analyze and view security data across your organization. Further, even though we just announced Cloud SCC a few weeks ago, already five container security companies have integrated their tools with Cloud SCC to help you better secure the containers you’re running on Google Kubernetes Engine.
Join this panel for a discussion with women product managers and engineers working at Google Cloud in infrastructure and containers.
Securing your infrastructure using open-source tools | Google Cloud Security Talks at RSA 2018
- Open source security
- Panel
Join our panel to explore open source security tools — what exists today, why building them is hard, how to start new ones, and what tools we still need.
Securing containers in production | Google Cloud Security Talks at RSA 2018
- Open source security
- Panel
A discussion of container security responsibilities throughout the lifecycle, from deployment to runtime, with practical tips for production environments.
Managing secrets in your cloud environment | BSidesSF 2018 | with Evan Johnson
- Secret management
- Encryption
Applications need secrets at build or run time. Cloud developers have many storage options — in code, environment variables, or purpose-built solutions.
Security overview | Google Cloud Montreal region opening
- Infrastructure security
- Encryption
- French
Maya Kaczorowski, Google Cloud Security & Privacy Product Manager, speaks at the opening of the Google Cloud region in Montréal.
At Google Cloud, customer data is encrypted at rest by default. Check out our video to learn all about the mechanisms used by Google to encrypt data at rest.
Watch this video to learn how Google Cloud encrypts data as it moves within and across Google Cloud datacenters.
Les leçons apprises de la sécurisation de Google et Google Cloud | Google Cloud Summit Paris | with Fenitra Ravelomanantsoa
- Infrastructure security
- Encryption
- French
La protection des données personnelles, la conformité et le GDPR sont des sujets centraux dans lesquels Google investit pour la sécuration des applications Google et de ses utilisateurs. Découvrez plus en détails ce que Google fait en termes de sécurité.
Protecting data in Google’s Cloud | Les Assises de la sécurité | with Julien Blanchez
- Infrastructure security
- Encryption
- French
Maya et Julien parlent de la manière dont Google protège la sécurité des données, et d’autres protections abordées aux données.
Learn more about Google’s infrastructure security, including encryption, network protections, and containers.
How Google encrypts data at rest at scale | Mundo Hacker Day 2017 | with Julien Blanchez
- Infrastructure security
- Encryption
Maya and Julien talk about how Google encrypts data at rest, and other data security protections in the cloud.
Can management of encryption keys be easier in the cloud than on-premise? During this video, Maya Kaczorowski discusses the continuum of encryption options available, from encryption of data at rest by default, to Cloud Key Management System, to Customer Supplied Encryption Keys. You’ll learn how our encryption tools allow management of your own keys, including generation, rotation and destruction of those keys. She also shares best practices for managing and securing secrets.
How data at rest is encrypted in Google’s Cloud, at scale | Cloudflare Crypto Meetup
- Encryption
How does Google encrypt data at rest? This talk will cover how Google shards and encrypts data by default, Google’s key management system, root of trust, and Google’s cryptographic library. Google Cloud Platform encrypts customer content stored at rest, without any action from the customer, using one or more encryption mechanisms. We will also discuss best practices in implementing encryption for your storage system(s).
Maya talks about how Google encrypts data, Google’s key management system, root of trust, and Google’s cryptographic library.
A look at Google’s encryption: how it shards and encrypts data, key management, root of trust, cryptographic libraries, and encryption best practices.